Protecting Infrastructure Against Terrorist Attacks

By Prostruct Consulting
Ang Choon Keat, Managing Director
Lin Yadong, Senior Executive Engineer, Security and Blast
Andrew Tan, Principal Engineer, Security and Blast
With the real possibility of terrorist threats, Singapore implemented the Infrastructure Protection Act (IPA) from December 2018, to provide a clear regulatory framework for protection against such threats. Selected buildings will have to undergo a security-by-design (SBD) process before they are built or renovated. This article gives a brief introduction of the IPA, the SBD process, as well as some common mitigation strategies to enhance building protection.
INTRODUCTION
Mitigating the threat of terrorist attacks has always been a challenging task. It is difficult to predict how, where and when such an attack will happen. A terrorist attack is an extremely disruptive force which can destabilize the normalcy and unity of a society. Historically, bombings have been among the favourite tactics by terrorists, as it is often the more effective way to gain media attention and create panic or shock to the public. Attacks can be carried out in forms of suicide bombers or by the detonation of vehicle borne explosives. Vehicles can also be driven at speed into groups of unsuspecting people.
Past terrorist incidents reflected that critical infrastructures are preferred target choices for terrorists. On 22 March 2016, three coordinated suicide bombings occurred in Belgium – two at Brussels Airport and one at Maalbeek metro station in central Brussels. The incident resulted in more than 30 fatalities and more than 300 injuries. On 10 December 2016, a car bomb and a bomb carried by a suicide bomber exploded in Istanbul killing 48 people and injuring several others. More recently, in November 2019, a suicide bomber targeted the Police Headquarters in the Indonesian city of Medan and blew himself up at the police station, killing himself and injuring several others in the process. In recent years, deliberate vehicle-ramming into crowds of people is becoming a major terrorist tactic, because it requires little resource and skill to perpetrate and has the potential to cause significant casualties. On 17 August 2017, a single perpetrator drove a van into a popular tourist pedestrian street in Barcelona, Spain killing 13 people and injuring at least 130 others.
Closer to home, a group of six militants were arrested after a planned attack to fire a rocket at Singapore’s Marina Bay Sands from Batam Island was foiled by the authorities in Aug 2016. If the attack was not uncovered and prevented, the consequences can be disastrous. Over the past few years, there has also been many arrests of individuals, either associated with terrorist groups or self-radicalised.
The Singapore Terrorism Threat Assessment Report, released by Ministry of Home Affairs (MHA) in June 20171, indicated that terrorism threat remains the highest to Singapore, in recent years. The potential terror threat has underscored the need for a more systematic way to protect key infrastructures. In response, the Infrastructure Protection Act (IPA) was passed on 2 October 2017, and came into force on 18 Dec 20182,3 as part of Singapore’s counter-terrorism efforts.
INFRASTRUCTURE PROTECTION ACT (IPA)
The IPA is intended to form a clear regulatory framework and comprehensive strategy to fight terror. Under the new law, MHA could designate new buildings as “special developments”, and existing buildings as “special infrastructures”. The designated buildings include those that provide essential services, have heavy human traffic or iconic or symbolic significance.
These identified buildings will be required to go through a “security-by-design” process to integrate security measures such as video surveillance, vehicle barriers and protection against blasts in their design before they are built, and for selected existing buildings to incorporate such measures in their renovation plans.
Security-By-Design (SBD)
Incorporating physical security concepts in the initial design of a new building or renovation plan for an upgraded building is often the most efficient and cost-effective way to achieve the required security level at minimal cost. In doing so, security can be effectively incorporated without compromising other objectives such as the functions and aesthetics of the buildings.
The main stages in SBD consist of the Preliminary Facility Design Development (PFDD), the Risk Assessment (comprising of the Threat, Vulnerability and Risk Assessment (TVRA) and the Blast Effects Analysis (BEA) and the development of a Security Protection Plan (SPP).The Security & Blast (S&B) Consultants commence the SBD study with the PFDD and the risk assessment. At this stage, S&B consultants will do a site appreciation to develop a preliminary security protection plan and to share applicable good security design practices.
The S&B Consultants will then work on the Threat, Vulnerability and Risk Assessment (TVRA) to determine the risks faced by the facility and specify the protection requirement. This is a systematic process to identify and analyze risks associated with applicable threats against the identified critical assets and how the threat scenarios may affect or impact the operations of the critical infrastructure. A BEA study will be conducted to determine the effects of a blast event and highlight any vulnerabilities.
Based on the results from TVRA and BEA, a Structural Resilience Study (SRS) will be conducted to recommend any mitigation measures required before putting up an SPP to achieve the necessary safeguards against identified threats.
The SPP will include layers of security protective measures that integrate physical & structural measures, technological measures and operational measures to mitigate the relevant security risks. A localised and outcome-based approach is usually adopted to determine the most appropriate security measures to mitigate those threats based on current capabilities and resource requirements.
PROTECTION PRINCIPAL AND RISK MANAGEMENT
Layered Protection Concept
Typically, a layered protection concept or “Defense-In-Depth” that involves layers of measures is adopted to enhance the security of buildings. These layers consisting of “Deter, Detect, Delay, Deny, and Response”4 complement each other through a combination of physical, operational and technological measures and provides a coordinated protection for a building. A multi-layered defense system is harder to penetrate as compared to a single layer of defense and it also gives security forces sufficient time to detect and respond to the incident as shown in Figure 1.
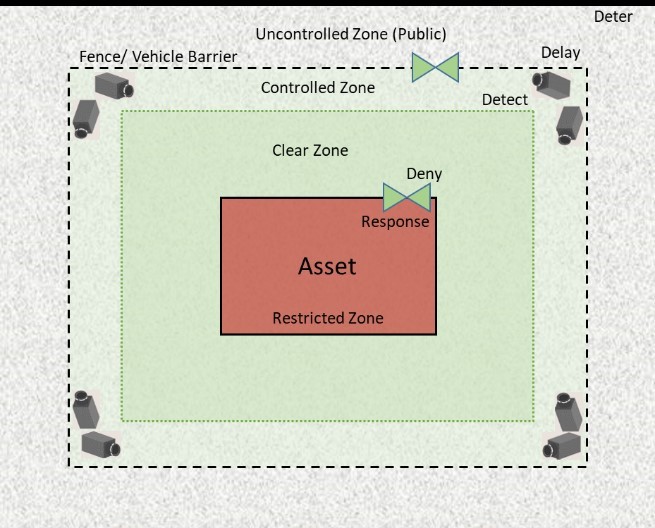
Figure 1: Layered Protection Concept
The deterrence layer provides the first impression of security level of the facility by making it clear to an adversary that the risk of failure or getting caught is high. It is an effect of visible physical security measures and making it an undesirable target.
Delay aims to slow down a perpetrator by using access control measures such as fence or physical barriers to make it difficult for the perpetrator to penetrate further into the facility.
Perpetrators who are not deterred must be dealt with. The detection layer facilitates the identification of threats, so an alert can be raised. Typical detection measures include video surveillance systems, electronic access control systems, magnetic contact and passive infra-red motion sensors, etc.
Deny ensures that only authorized persons are allowed entry into protected areas. This can be achieved through card access systems or deploying security guards at access control points.
Response refers to the means taken to counter an attack, so as to protect important assets. Response measures can include activation of security systems, including but not limited to, alarm system and dispatching of security personnel.
Risk Management Approach
A risk management approach as shown in Figure 2 is recommended to ensure appropriate security measures are in place to address relevant threats. Risk management approach involves assessment of threat scenarios and consequences against existing security baseline measures. Then, further protection measures to mitigate these risks such as operational measures, technological measures and hardening of critical assets can be calibrated for implementation.
This Security Protection Measures and Plan should be reviewed periodically to ensure that the security measures are sufficient to mitigate emerging or evolving threats as the security climate change in the future.
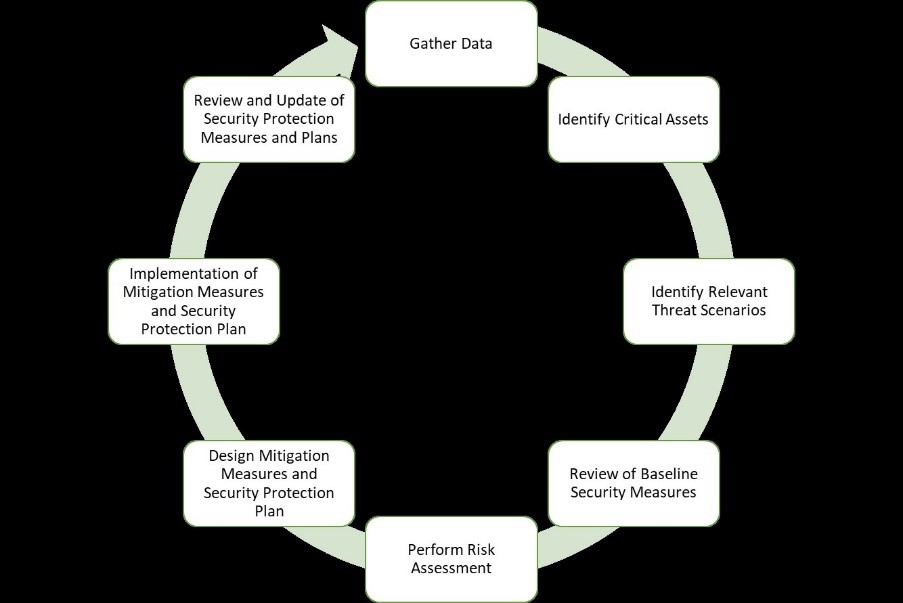
Figure 2: Risk Management Cycle
Increasing Standoff Distance
Protection of a building from an explosion occurring outside the building is achieved by increasing the standoff distance from the bomb threat and strengthening the building against blast and other effects of an explosion5. Some of the common measures include traffic flow and access control by setting up anti-ram vehicle barriers or bollards to increase standoff distances, hardening of structural components to withstand blast loadings, locating critical assets away from public areas to reduce their vulnerabilities, and hardened protection at vulnerable openings that are exposed to blast threats.
Increasing standoff distance between the building and potential bomb threats is perhaps the most effective strategy of mitigating damage to the building. As standoff increases, the blast loads generated by an explosion decrease and the amount of hardening necessary to provide the required level of protection decreases. In addition, the cost to provide asset protection will decrease as the distance between an asset and a threat increases, as shown in Figure 36.
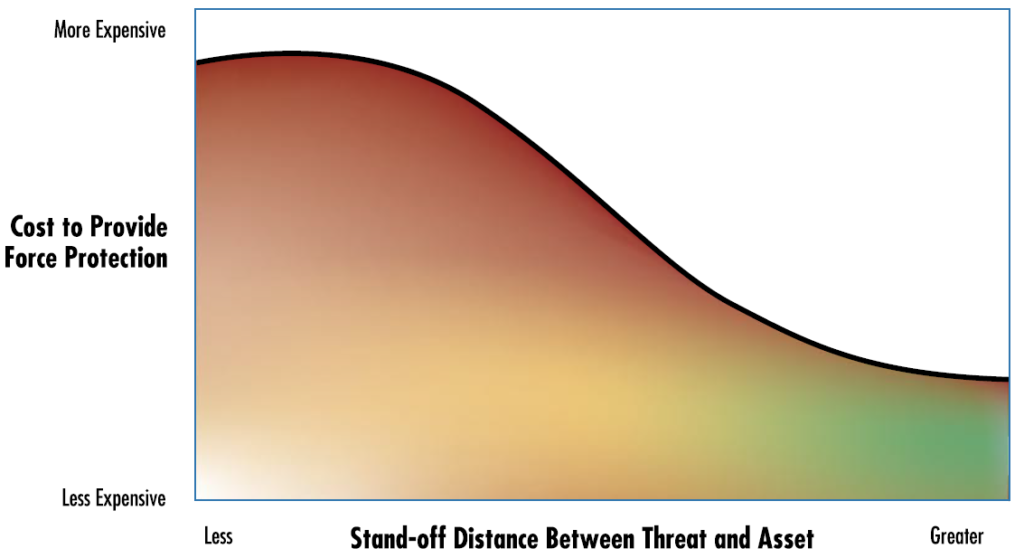
Figure 3: Relationship of cost to stand-off distance (Source: FEMA 426)
Where possible, this can be achieved via measures such as bollards (Figure 4), barriers, landscaping, etc. The bollards/barriers need to be anti-crash, in order to withstand crash impacts and prevent entry of offensive vehicles.

Figure 4: Bollards to create additional standoff
A properly designed anti-crash system7,8 denies a vehicle from getting nearer to the protected building. It can also serve as a psychological strategy which reduces a threat probability and vulnerability by making it clear to an adversary that the risk of attack failure is high. This deterrence and denial layer form a protection layer that is away from the protected asset. It provides a visible physical security measures and clear warnings that the building is protected. The bollards/barriers can be further complemented by other protection measures such as detection technology along the perimeter/barriers, coupled with adequate lighting and response measures such security personnel, to form a complete layered protection for the building.
Structural Hardening
In some cases, increasing standoff distances is insufficient or unavailable to mitigate the blast effects. It may be necessary to adopt designs to prevent progressive collapse of the entire building. Progressive collapse is defined as the spread of an initial local failure from element to element, eventually resulting in the collapse of an entire building. The Oklahoma City bombing (April 1995) is an example that illustrates the importance of designing buildings to prevent progressive collapse. In that incident, most of the deaths resulted from the collapse of the building, as opposed to the bomb blast itself.
Preventing progressive collapse through structural hardening is also crucial in protecting the interior inhabitants and critical assets to ensure minimal casualties, and continual operations of essential services to minimize disruptions to operations.
Structural hardening measures could come in various forms. The straight forward way is simply to increase the physical size of the structural components and/or the reinforcement details until they are sufficiently thick and can therefore resist the blast loads. Alternatively, the strength of structural components can also be increased by other means such as external strengthening with Fiber Reinforced Polymers (FRP) composites (Figure 5).

Figure 5: Strengthening of structures with FRP composites
Protection of Openings
Openings refer to locations in a building, that provide access for equipment and personnel, and which are covered by doors, roller shutters or windows. When an explosion occurs outside the building, these openings become the vulnerable points where blast and flying fragments could enter and cause damages to assets or injuries to occupants.
Conventional mitigation solutions involve installing blast resistant doors (Figure 6). Due to certain operation limitations of blast doors, blast roller shutter doors (Figure 7) have also been explored by the industry in recent years for protection of larger openings.

Figure 6: Blast door, commonly installed at protected building openings

Figure 7: Blast Roller Shutter door, for protection of large openings
SUMMARY
In summary, the IPA was implemented in Dec 2018 as part of the nation’s counter-terrorism strategy to keep Singapore safe and secure. It means selected buildings would have to go through a vigorous SBD process to incorporate security measures upfront.
This article introduces the strategies and common mitigation measures to protect buildings from explosions. A multi-layered defense system which includes creating standoff distances, hardening of structural components and protection of vulnerable openings are commonly adopted measures to mitigate the relevant security risks. However, one should note that these common measures shall be customized and may not be applicable for all scenarios as threats and protection criteria are unique to every different building.
In many cases, it is often necessary to combine several solutions to achieve full protection. At times, it would require the industry to innovate and offer new protective technologies that are more effective and/or economical.
This article was first published in “The Singapore Engineer (April 2018)”.
Connect with Us
Ang Choon Keat
Email: [email protected]
Lin Yadong
Email: [email protected]
Andrew Tan
Email: [email protected]
References
[1] Ministry of Home Affairs (2017, Jun 1). Singapore Terrorism Threat Assessment Report 2017 [Press release]. Retrieved from: https://www.mha.gov.sg/newsroom/press-releases/Pages/Singapore-Terrorism-Threat-Assessment-Report-2017.aspx


